Attacks on IT environments are becoming increasingly sophisticated and harder to detect using traditional cybersecurity methodology. It is no longer enough to rely on stopping threats by monitoring an IT environment for intrusions by previously identified malware or known exploitation patterns. Proactive measures need to be taken to identify new and emerging threats to effectively protect an organization’s business-critical systems and valuable data resources.
Addressing the need to identify emerging threats requires technical solutions that can collect and evaluate available information to recognize risks that can impact the environment. An extended detection and response (XDR) platform makes use of threat intelligence to discover and respond to previously unknown threats before they can cause damage to the infrastructure.
What is Threat Intelligence?
The NIST defines threat intelligence as threat information that has been aggregated, transformed, analyzed, interpreted, or enriched to provide the necessary context for decision-making. Data used to provide threat intelligence can come from a variety of sources including social media interactions, cybersecurity or antivirus logs, and monitoring online activity to spot suspicious behavior.
Threat intelligence (TI) can be categorized in four ways based on the specific type of information it provides and how it is communicated to its intended audience. A comprehensive threat assessment includes consolidating all four types of TI.
- Strategic threat intelligence - This type of TI is focused on summarizing possible cyberattacks and their effects by analyzing trends and emerging threats. Strategic TI gives an organization an overview of its threat landscape. It is communicated via white papers or reports designed for consumption by non-technical audiences and organizational decision-makers.
- Tactical threat intelligence - Tactical TI provides the individuals responsible for protecting the IT environment with information concerning the tactics and methods used by threat actors. Cybersecurity personnel use this information to understand how they may be attacked and the best way to defend the organization.
- Technical threat intelligence - This kind of TI concentrates on indications that an attack is underway. Technical TI can be instrumental in minimizing attacks based on social engineering. It looks for signs that threat actors are performing reconnaissance before delivering malware or initiating an attack.
- Operational threat intelligence - Operational TI incorporates information from a wide range of sources to predict when and how future attacks will be conducted. It leverages the power of machine learning and data mining to automate the evaluation of large volumes of data. This type of TI provides security teams with information that can be used to update system configuration and access controls to protect the environment.
What is the Threat Intelligence Lifecycle?
Cyber threat intelligence (CTI) programs typically involve an established lifecycle comprising the following six phases.
- Planning and direction - An organization needs to select threat intelligence solutions based on its goals for the program. In most cases, they want TI that is related to emerging and high-risk threats to their business. An additional objective is to provide the strategic TI necessary to convince management that cybersecurity measures need to be strengthened.
- Collection - Data is collected from a variety of sources including system logs and security controls. Third-party threat data such as that provided by NTT’s Tier 1 internet backbone adds depth to the collected data and is essential for effective threat detection.
- Processing - Automated processing is required to turn the raw data collected into actionable threat intelligence. Machine learning is often incorporated into TI solutions to facilitate efficient data processing.
- Analysis - Analyzing TI can be performed by humans or artificial intelligence platforms. The analysis informs decisions about where and when potential attacks may occur and how to efficiently address the risk. Effective TI requires this information to be delivered to the appropriate personnel in easily understandable language.
- Dissemination - The information derived from TI needs to be disseminated to the teams responsible for protecting the environment. Decisions such as how best to deliver the information, the format employed, and how often to update it are essential aspects of making productive use of TI.
- Feedback from CTI consumers - Finally, feedback from the TI audience needs to be considered to determine if modifications need to be made in how information is collected, processed, or disseminated.
Why is Threat Intelligence Essential for Effective Cybersecurity?
Threat intelligence is necessary to keep up with the pace of change in the cyber threat landscape. Without reliable threat intelligence, businesses are vulnerable to emerging risks that have not yet been codified and incorporated into antivirus definitions or firewall rules.
The different types of threat intelligence affect different areas of a business.
- Strategic threat intelligence allows an organization to better understand its risks and can be instrumental in influencing decision-makers to focus more resources on cybersecurity.
- Tactical threat intelligence is most useful to the individuals responsible for cybersecurity. It allows them to understand the methods used by threat actors and better prepare adequate defenses to protect the environment.
- Technical threat intelligence can be used by the cybersecurity team or system administrators to identify abnormal behavior and other signs that an attack is imminent.
- Operational threat intelligence gives the organization information that can be used to develop and implement stronger cybersecurity measures to address new risks to the environment.
Taken together, the different forms of TI help an organization defend itself from sophisticated threat actors.
How Samurai XDR Leverages Advanced Threat Intelligence
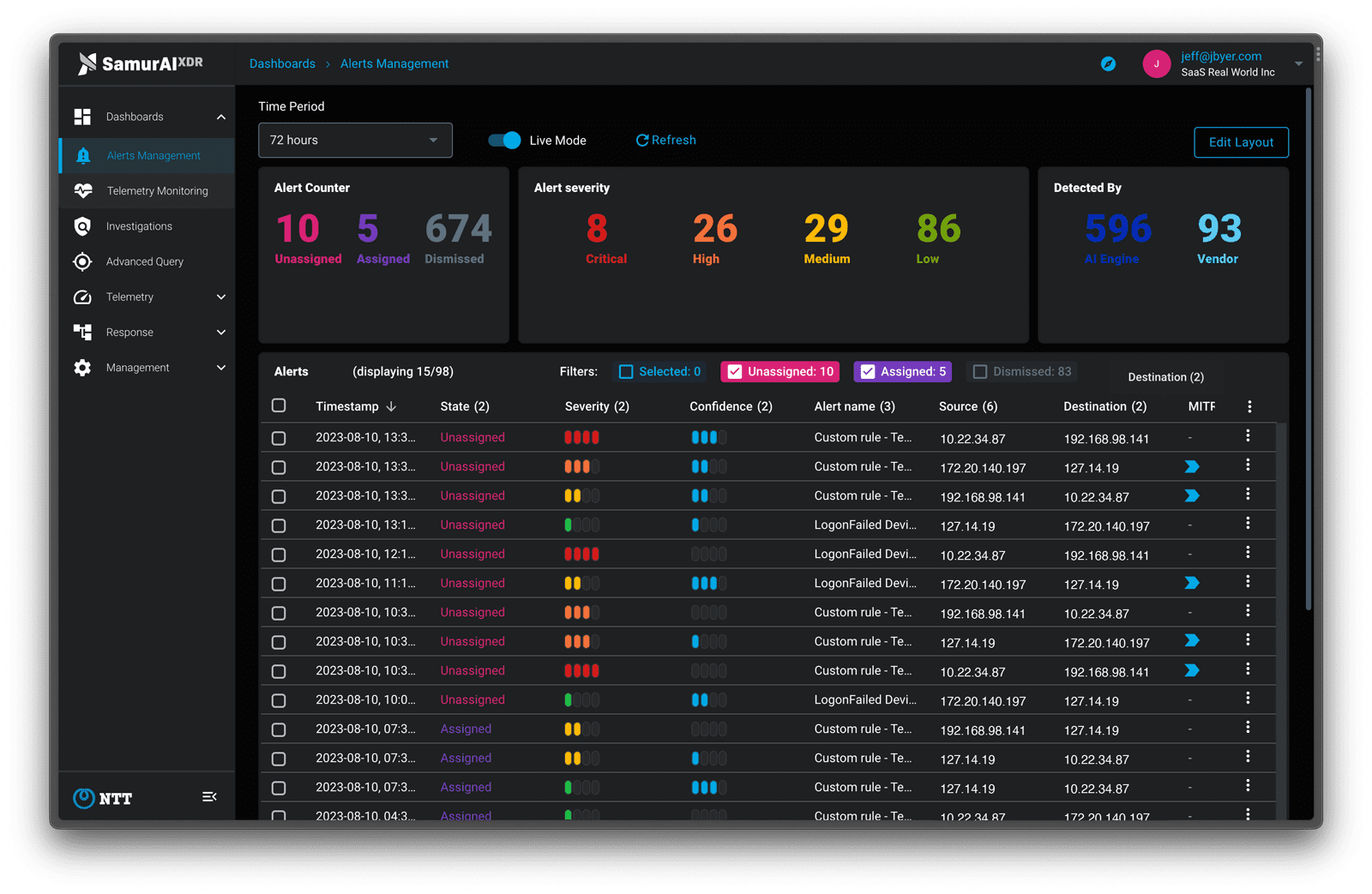
Samurai XDR leverages advanced threat intelligence to provide simple and cost-effective enterprise-grade detection and response functionality.
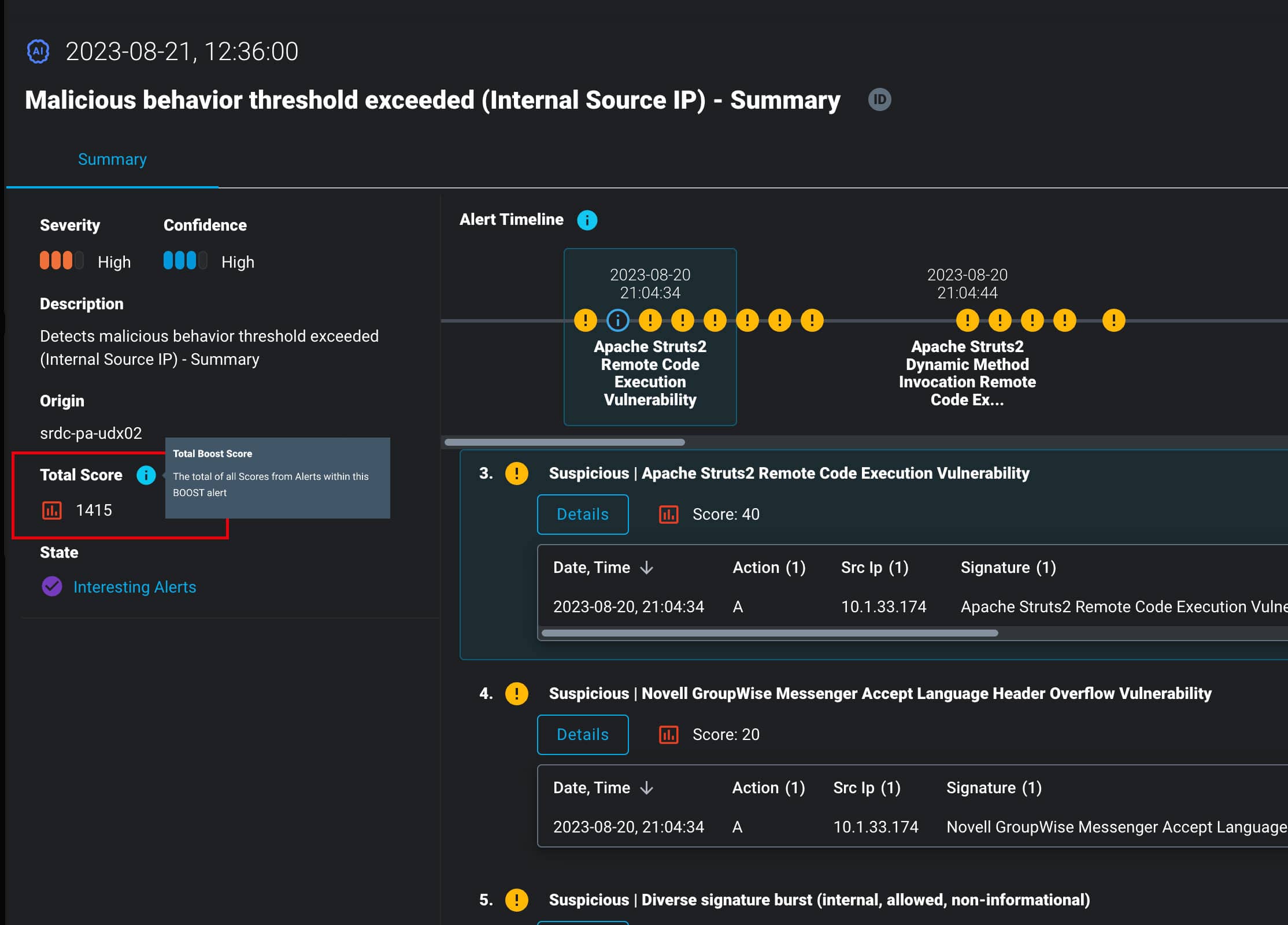
- The XDR platform uses threat intelligence as the basis for the AI and ML analysis that detects known and unknown threats before they can impact the environment. The tool then prioritizes identified threats to allow security personnel to address them more efficiently and protect enterprise IT resources.
- Samurai XDR’s detection engine employs NTT’s Tier 1 internet backbone to provide a unique perspective on new and emerging threats. This IP backbone is one of the largest in the world and provides visibility on over 40% of global internet coverage. NTT is a global leader in cybersecurity, trusted by many of the world’s most prestigious organizations.
- Samurai XDR integrates the threat intelligence from NTT’s T1 backbone directly into the platform. This eliminates the need for companies to supply an independent source of threat intelligence and coordinate its use with separate tools. In addition to promoting the efficient use of threat intelligence, this approach is cost-effective and reduces unnecessary complexity.
Customers can contact the threat detection experts at Samurai and request a free trial.
Featured articles
Identity Management in the Physical and Digital Worlds
7 August 2024 | Webinars
In today's rapidly evolving world, managing identities securely and efficiently is more crucial than ever. Join us for an insightful...
Identity Management in the Physical and Digital Worlds
30 July 2024 | Webinars
In today's rapidly evolving world, managing identities securely and efficiently is more crucial than ever. Join us for an insightful...
XDR for Small and Medium Businesses: Is It Worth It?
24 July 2024 | XDR
Cybersecurity is of paramount importance to virtually all organizations and SMBs have to address several specific challenges. The failure to...





