The threat landscape affecting an organization’s IT environment is constantly changing. Threat actors working alone or in organized groups are continuously looking for new methods and techniques with which to exploit vulnerabilities in a computing environment to compromise business-critical systems and valuable data resources.
Why Advanced Threat Detection is Required for Effective Security
The rapid pace at which new threats are developed and exposed to IT environments makes them impossible to address using traditional cybersecurity measures. Typically, legacy cybersecurity tools are based on preventing known threats from accessing systems and causing damage. This is usually accomplished by scanning for the digital signatures of known malware and viruses.
Threat actors have increasingly refined the techniques they use to exploit an IT environment. Subtle intrusions can result in advanced persistent threats (APTs) that can linger in a system and compromise data resources for years. Malicious entities are taking advantage of technological developments such as generative AI to construct new and dangerous threats.
The sophisticated nature of modern threat actors has made traditional cybersecurity techniques obsolete. While solutions such as firewalls and antivirus software still play a part in protecting an IT environment, new techniques must also be incorporated to provide effective security. It’s not enough to simply stop known threats from affecting the infrastructure.
Advanced threat detection incorporates artificial intelligence and machine learning to conduct extensive behavioral analysis that can uncover previously unknown threats. An extended detection and response (XDR) platform is capable of identifying the subtle lateral movements in an IT environment that indicate the presence of an APT or other type of threat actor.
How Samurai XDR Provides Enhanced Threat Detection
Samurai’s XDR solution provides the enhanced threat detection organizations need to counteract the sophisticated methods of modern threat actors. It is a software-as-a-service (SaaS) offering that is easy to implement and integrates smoothly with your current cybersecurity stack.
Samurai XDR is focused on detecting known and emerging threats so they can be investigated and mitigated by the individuals responsible for a company’s cybersecurity. The ability to detect threats before they have a chance to impact the environment is critical in defending against today’s sophisticated threat actors. The failure to proactively address new threats risks losing access to business-critical systems and sensitive data.
The following features and characteristics of Samurai’s XDR solution make it an excellent platform for efficiently detecting threats and protecting an organization’s valuable systems and data resources.
Superior Threat Intelligence
The foundation of Samurai XDR’s detection engine is NTT’s Tier 1 internet backbone which monitors over 40% of the world’s internet coverage. This unique knowledge base provides Samurai XDR with advanced threat intelligence (TI) which promotes enhanced detection and response capabilities that quickly address emerging threats.
This comprehensive TI feed provides more context and data enrichment than publicly available threat feeds. Additional TI information is provided by insights and research from our GTIC team, along with indicators from our MDR service. The extensive reach provided by NTT’s internet backbone and the number of sources it queries to gather TI gives Samurai a distinct advantage over other XDR solutions that only rely on public feeds.
Integration with Multiple Telemetry Sources
Effective threat detection requires telemetry to be collected from a wide variety of sources that affect the environment. Employing more telemetry sources provides additional raw material with which Samurai XDR can evaluate threats by searching for suspicious behavior or malware identified through its extensive repository of TI. Drawing a complete picture of the infrastructure is essential for effective threat detection.
Samurai XDR’s integration facility makes it easy for customers to gather and consolidate telemetry from throughout the environment. Customers can leverage supported integrations incorporated into the platform to collect telemetry from existing firewalls and endpoint defenders.
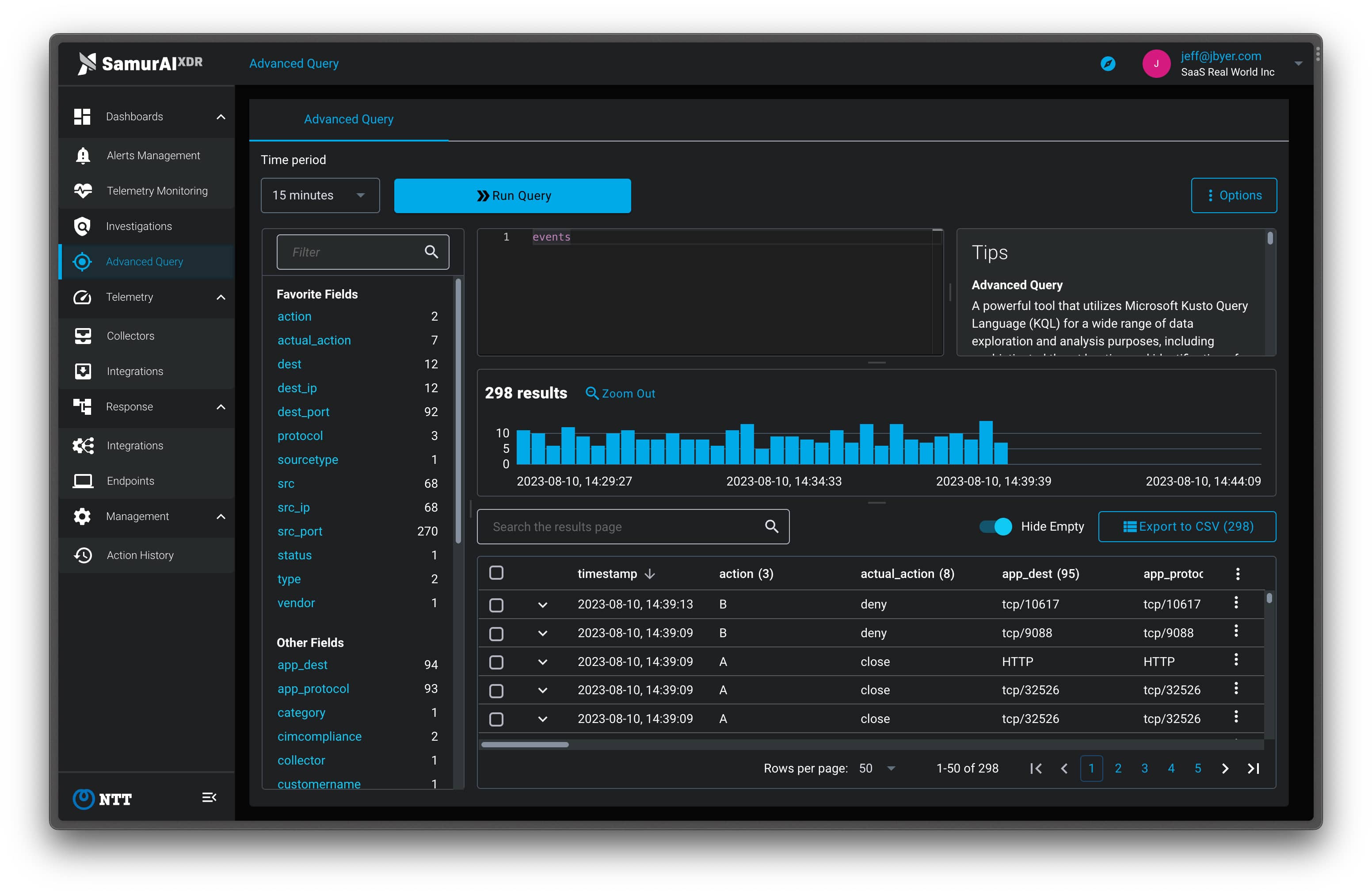
In addition to Samurai’s supported integrations, the platform can handle generic log sources by ingesting the information into its data lake for use in threat detection. In cases where this additional data cannot be used directly by the tool to generate alerts, the data can be analyzed with Samurai’s Advanced Query feature. Customers can use advanced queries to analyze syslog data that contains basic information such as a timestamp and the identities of the collector and source that generated the event in question.
Advanced Analytics and Machine Learning
Through advanced analytics and machine learning, the platform can analyze large volumes of telemetry efficiently. This analysis is instrumental in identifying abnormal behavior that may indicate the presence of a threat. The volume of data necessary to perform efficient threat detection cannot be processed manually.
Samurai’s advanced artificial intelligence and machine learning promote continuous improvement in the XDR solution. As new threats or methodologies are detected and their characteristics incorporated by the platform, it becomes more proficient at identifying threats to the environment. Samurai XDR is designed to protect your infrastructure today and into the future.
Cutting-Edge Functionality
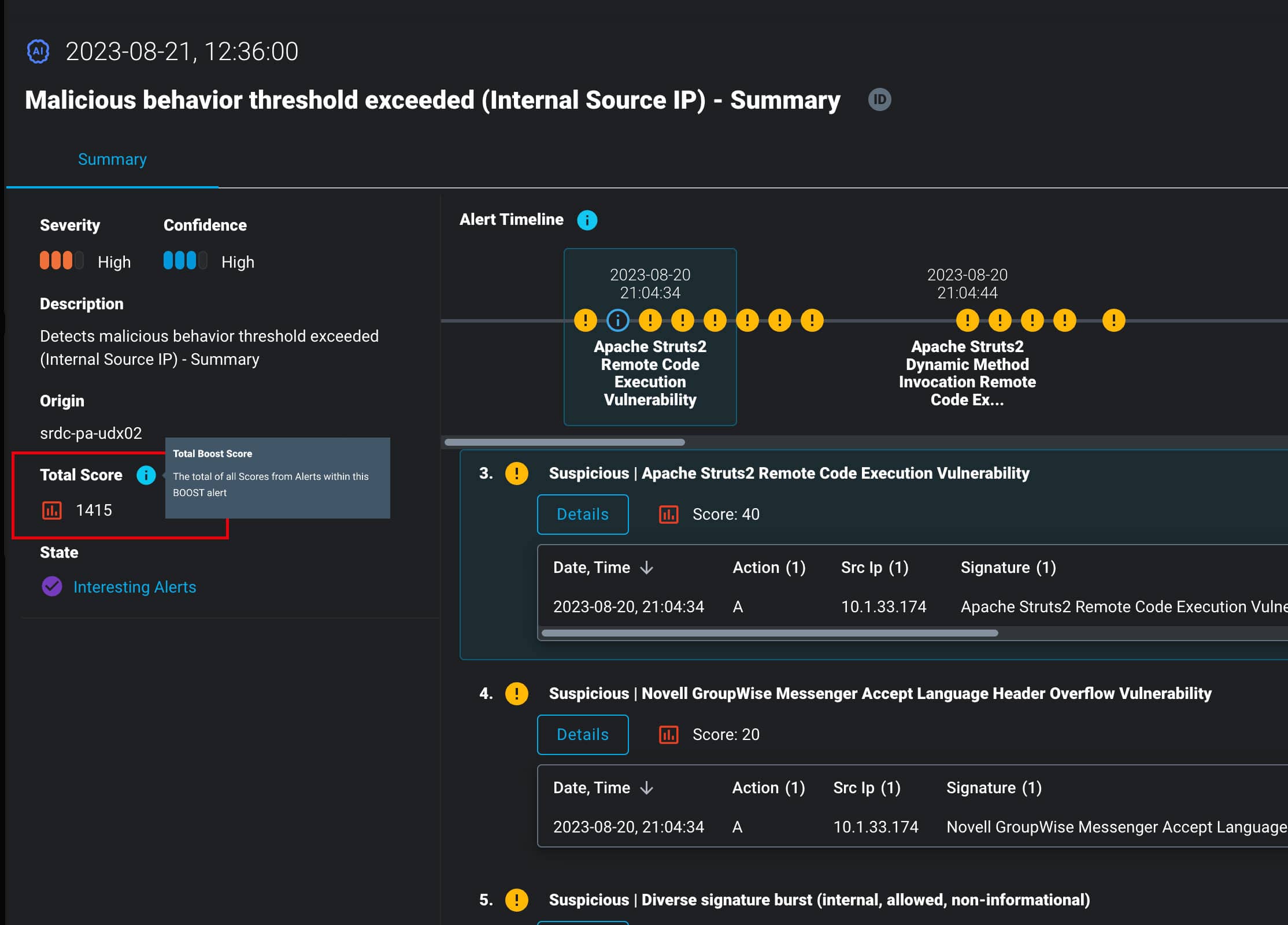
Advanced techniques such as Samurai’s Boost Scoring enable the platform to prioritize and focus on the most important and impactful threats. Boost scoring improves the ability to identify APTs by consolidating insights from multiple sources. This enables Samurai to detect activities that do not pose threats by themselves, but in combination may represent serious danger to the environment. The functionality provided by boost scoring also is effective in identifying dormant or slow-moving attacks that may escape detection through other methods.
Samurai XDR removes false positives that can result in wasted time and alert overload. By prioritizing the threats that are potentially more dangerous to the infrastructure, the platform increases the effectiveness and productivity of even a small cybersecurity team.
A Team of Threat Research Experts
The threat intelligence technology that powers Samurai XDR is continuously being improved by a team of threat research experts in its Global Threat Intelligence Center. The team is staffed with experienced threat intelligence analysts who employ multiple custom tools and methods to track emerging threats and the vulnerabilities they look to exploit. The TI generated by this team is proprietary to Samurai XDR and gives it an edge over competing platforms.
Conclusion
Taken together, the advanced features available in Samurai XDR efficiently and effectively detect the sophisticated entities that threaten your business. The platform complements your existing cybersecurity defenses with threat detection capabilities that protect against current risks and those yet to be devised by malicious threat actors.
Customers interested in the superior capabilities of this cybersecurity platform should contact the threat detection experts at Samurai to see how XDR seamlessly integrates with your existing cybersecurity measures. Request a free trial to see the solution in action and learn how it can help defend your organization from sophisticated threats.
Featured articles
Identity Management in the Physical and Digital Worlds
7 August 2024 | Webinars
In today's rapidly evolving world, managing identities securely and efficiently is more crucial than ever. Join us for an insightful...
Identity Management in the Physical and Digital Worlds
30 July 2024 | Webinars
In today's rapidly evolving world, managing identities securely and efficiently is more crucial than ever. Join us for an insightful...
XDR for Small and Medium Businesses: Is It Worth It?
24 July 2024 | XDR
Cybersecurity is of paramount importance to virtually all organizations and SMBs have to address several specific challenges. The failure to...





