Whaling is a targeted form of spear phishing that focuses on an organization’s high-profile targets and senior executives. It is a type of cyberattack that employs social engineering tactics in an attempt to entice the target into performing a secondary action that can be extremely detrimental to them personally or cause damage to their company.
The term whaling refers to the size or importance of the victim. These attacks are designed to be substantially more lucrative to the cybercriminals if successful. Referring to the targets as whales is based on their role or importance to their organization and may have been borrowed from casino parlance describing gamblers with deep pockets.
We’re going to look at the details of whaling attacks, what they hope to achieve, and strategies for minimizing their chances of success.
How Whaling Differs From Generic Phishing
Several differences between generic phishing and whaling make the latter much more dangerous to the victim and their organization.
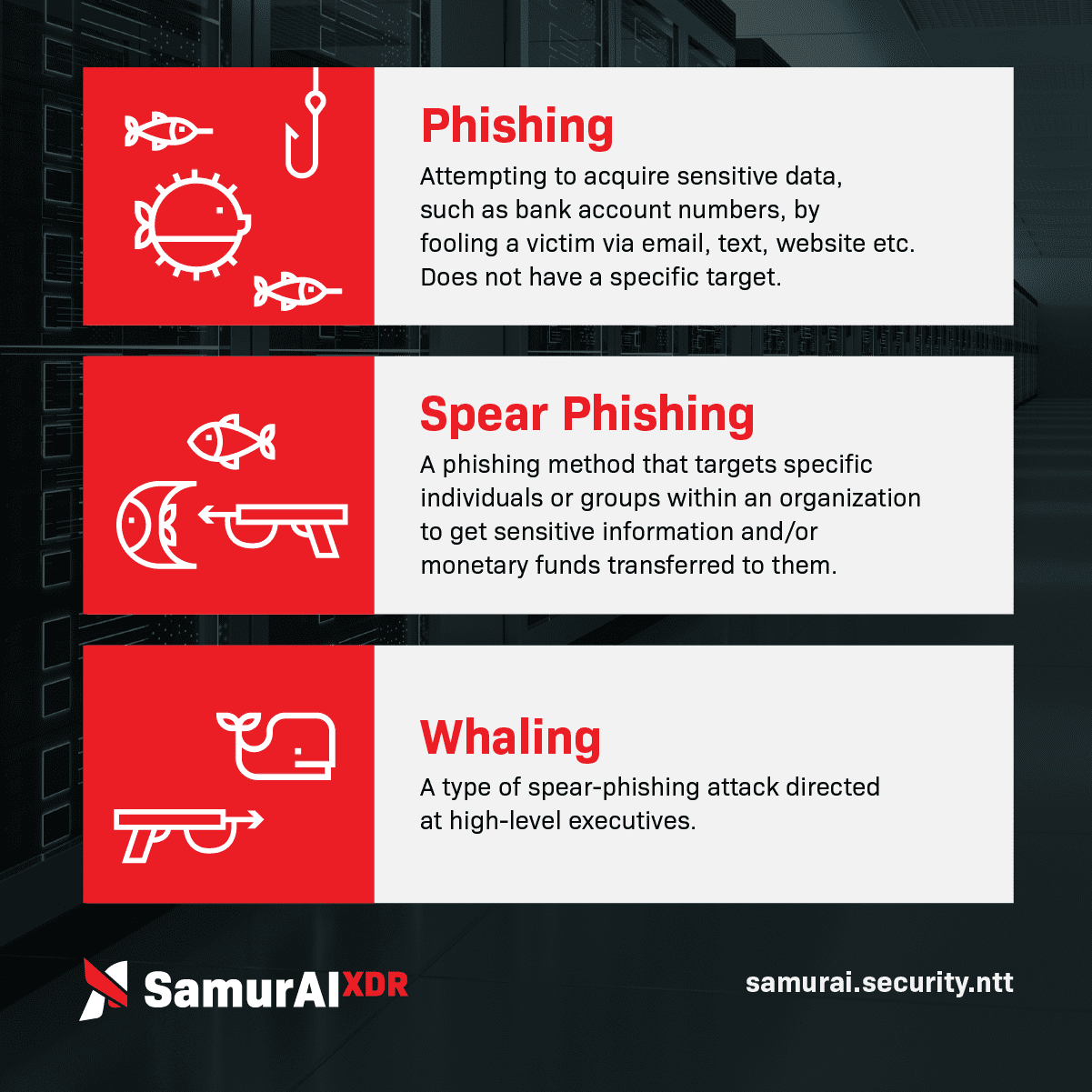
In a generic phishing attack, cybercriminals send the same email or text message to a large number of anonymous recipients. The hope is that some of the recipients will be fooled by the message and perform actions that compromise security or put assets at risk. If only a small percentage of the recipients fall for the scam, the criminals deem it a success.
The targets of whaling attacks are chosen selectively based on their role in an organization and the potential gains that threat actors can extract from them if successful. Fraudulent messages sent to these recipients are carefully crafted to appeal directly to them. In many cases, the attacker impersonates an associate of the intended victim to gain their trust.
Selectively targeting victims reduces the potential quantity of successful attacks, but increases their quality from the perspective of cybercriminals. A single successful whaling attack can be extremely lucrative for its perpetrators.
How Threat Actors Identify Whaling Targets
Whaling targets can be identified by threat actors in various ways. The following methods are used to find the right targets.
- Publicly available information can be used to identify a company’s senior management and executives. In some cases, contact information such as email addresses or phone numbers may also be easily obtainable.
- Social media sites such as LinkedIn provide information on their members that can be used to identify whaling targets.
- Information from former or current employees can be leveraged for whaling. In addition to identifying high-profile personnel, insiders can provide details regarding email addresses or specific information the whaling correspondence should include to achieve the best results.
How a Whaling Attack is Conducted
Once the potential victim of a whaling attack is identified, the attackers may use multiple methods to attain their goals. Following are the most common techniques used in whaling attacks.
- Email or text messaging is often used to initiate contact between the attacker and the victim. The victim is implored to download a file or transfer funds that are urgently needed to address an emergency.
- Phone calls are used to further convince the victim to take the requested action if they are not responding to the email promptly. The additional pressure of repeated calls may sway a skeptical victim that they should take the requested action.
- Baiting is a tactic that plays on the interests of the victim in an attempt to get them to compromise security. For instance, a threat actor may leave a thumb drive containing malware and labeled NBA Finals 2018 on the desk of an executive who is a great basketball fan. The hope is that they will insert the drive into a command machine and potentially infect the network.
Objectives and Outcomes of Whaling Attacks
The primary objective of a whaling attack is to convince the victim to perform a specific action defined by the attackers. Underlying reasons for an attack include:
- Financial gain;
- Supply chain attacks;
- Corporate espionage;
- Malware delivery;
- Obtaining control over infrastructure components;
- Personal attacks against the victim.
The damages caused by successful whaling attacks can be extremely harmful to the individual and their organization. They include:
- Financial losses in response to fraudulent requests to transfer funds;
- Data loss arising from compromised credentials;
- Reputational damage by exposing sensitive information or intellectual property.
Why Whaling Attacks Are Particularly Dangerous
Whaling attacks are generally more dangerous than ordinary phishing attempts because the high-value targets have access to business-critical information and the ability to make quick decisions that can negatively affect a company.
Upper management can decide to move large sums of money that lower-level employees cannot approve. Compromising the credentials of a CIO will typically provide threat actors with a greater potential to cause damage than they would by stealing the password of a junior programmer.
High-profile targets can make quick decisions that affect the future of their organization. As you will see in the following examples, substantial damage can occur in the wake of a whaling attack.
- Snapchat - This attack was directed at the company’s HR staff and was the result of an email fraudulently attributed to the CEO. The phony CEO requested information regarding payroll information about current and former employees. No customer data was revealed in this attack.
- Scoular - In this case, Scoular’s corporate controller was targeted with fake emails purportedly from the company’s CEO and other entities involved in a fictitious company acquisition. The attack netted the perpetrators over $17 million.
Preventing Successful Whaling Attacks
Whaling attacks can be prevented by implementing the following best practices.
- Provide security awareness training for upper management. As the targets in whaling attacks, these individuals need to know what to look for and how to avoid falling victim to sophisticated social engineering attacks.
- Implement organization-wide verification processes that make it impossible for a single individual to move funds.
- Perform email scanning and filtering to reduce the chances of a whaling attempt reaching its intended victim's inbox.
- Invest in anti-impersonation software to reduce the chances of whaling attempts getting to their targets.
- Perform DNS authentication on the sender’s domain to identify and remove messages from spoofed addresses.
How XDR Limits the Damage of a Whaling Attack
The preventative measures discussed above necessarily form the initial lines of defense against whaling. Ideally, the prospect of successful whaling attempts is eliminated through security awareness and robust email hygiene. Unfortunately, even the best cybersecurity defenses can be breached by sophisticated threat actors.
When the purpose of a whaling attack is to plant malware in the environment, XDR can be instrumental in limiting the damage. XDR limits the damage of a malware attack by:
- Providing visibility into the complete digital estate and consolidating weak signals that may indicate malware infection;
- Identifying lateral movement throughout the environment that often accompanies sophisticated attacks and advanced persistent threats (APTs);
- Warning security personnel of suspicious behavior that may indicate threat actors are present in the environment.
XDR provides a sophisticated and comprehensive method of identifying and responding to the evolving techniques of threat actors. Let the experts at Samurai show you how XDR can address threats introduced into the environment that escape detection from traditional security solutions.
Featured articles
Identity Management in the Physical and Digital Worlds
7 August 2024 | Webinars
In today's rapidly evolving world, managing identities securely and efficiently is more crucial than ever. Join us for an insightful...
Identity Management in the Physical and Digital Worlds
30 July 2024 | Webinars
In today's rapidly evolving world, managing identities securely and efficiently is more crucial than ever. Join us for an insightful...
XDR for Small and Medium Businesses: Is It Worth It?
24 July 2024 | XDR
Cybersecurity is of paramount importance to virtually all organizations and SMBs have to address several specific challenges. The failure to...





